- PA-213: Palo Alto Networks Firewall Install, Configure, and Manage (EDU-201)
- PA-212: Palo Alto Networks Firewall Configure Extended Features (EDU-205)
- PA-215: Palo Alto Networks Firewall Essentials FastTrack
- PA-232: Palo Alto Networks Panorama Manage Multiple Firewalls (EDU-221)
- PA-242: Palo Alto Networks Firewall Manage Cyberthreats (EDU-231)
- PA-243: Palo Alto Networks Firewall Debug and Troubleshoot (EDU-311)
Course Overview:
This Python for Penetration Testing course is designed to give you the skills you need for maintaining or developing Python Penetration Testing tools oriented towards offensive operations. We have a suite of courses and certifications that help understand a problem, this course prepares the student to rapidly develop prototype code to attack or defend against it.
The course concludes with a Capture the Flag event that will test both your ability to apply your new tools and coding skills in a Python Penetration Testing challenge.
This course is not intended to be an Advanced Python course, but to exemplify penetration techniques utilizing Python. The course covers Threading, Sockets, OOP, and third party modules that facilitate the offensive operator’s objective.
This course utilizes the “Violent Python” text book.
Attendees to TN-345: Python for Penetration Testers Class will receive TechNow approved course materials and expert instruction.
Dates/Locations:
No Events
Duration: 3 Days
Course Objectives:
- Python Lanuage Refress
- Network Sockets
- Exception Handling
- Hashes and Cracking Passwords
- Threading
- Concepts and Python Implementation
- Queues and Synchronization
- urlparse and httplib to probe URLs
- Crack a password protected zip file
- Port Scanner
- Threading a Port Scanner
- nmap integration
- Deploying shellcode
- Mechanize, BeautifulSoup
- HTTP Form Password Guessing
- HTTP Proxies (Burp Suite)
- HTTP Cookies Session Hijacking
- CookieMonster
- Images and Metadata
- Justniffer
- SQL Injection
- sqlmap
- SQLBrute
- Antivirus and IDS evasion
- PyInstaller
- Metasploit
- Scapy
- Deploy shellcode
- DNS Cache Poisoning
- Packety Violence
Prerequisites:
- Python Programming Skills or P-325: Python Programming
Comments
Latest comments from students
Liked the class? Then let everyone know!
Here are the Cisco Security course offerings:
- N-305: CCNA Bootcamp
- N-325: Implementing Cisco IOS Network Security (IINS)
- N-415: Implementing and Operating Cisco Enterprise Network Core Technologies (ENCOR)
- N-425 : Implementing Cisco Enterprise Advanced Routing and Services ( ENARSI)
- N-485: In-Depth Securing Networks with Cisco Firepower Threat Defense NGFW
- TN-865: Wireshark Network Traffic and Security Analysis
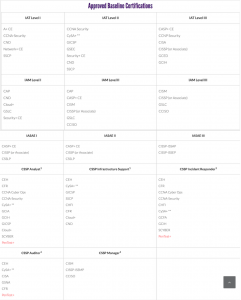
DoD 8570 Training
The Department of Defense requires that all information assurance personnel must become compliant with IT and security certification standards.
DoD 8570 training, also called Information Assurance training, is available through TechNow to provide you with the certification that is required. Your DoD 8570 training ( information assurance training ) at TechNow will provide you with all of the courses necessary to receive your DoD 8570.01-M certification.
Ongoing open enrollment through TechNow is available for our DoD 8570.01-M courses.
Please review the full & updated DoD approved IA baseline certifications aligned to each category & level of the IA workforce.
- CL-315: CCSP – Certified Cloud Security Professional Preparation Seminar
- CT-205: A+ Certification Course
- CT-208: A+ Extended Boot Camp
- CT-225: Network+
- CT-325: Security+
- CT-395: CySA+ Cybersecurity Analyst
- CT-425: CompTIA SecurityX
- TN-415: Computer Hacking Forensics Investigator (CHFI)
- TN-545: Certified Network Defender
- TN-555: Certified Ethical Hacker v13 (CEH)
- TN-715: Systems Security Certified Practitioner (SSCP)
- TN-812: Information Systems Security Engineering Professional (ISSEP)
- TN-813: Certified in Governance, Risk and Compliance (CGRC)
- TN-8150: CISSP Certification Preparation Seminar
- TN-822: Certified Information Systems Auditor (CISA) Seminar
- TN-825: Certified Information Security Manager (CISM) Seminar
- TN-835: Certified in Risk and Information Systems Control (CRISC) Preparation Seminar
- TN-865: Wireshark Network Traffic and Security Analysis
For further information or to schedule for classes, call us at 800-324-2294
Course Overview:
This course identifies how business analysts can elicit Agile requirements by writing user stories from use cases and personas of customer profiles. This leads to the processes of confirming the validity and usability for quality of the product development. An Agile Business Analyst has become a new recognized role within the other Agile Framework roles.
Attendees to PM-242:Defining Agile Requirements with User Stories will receive TechNow approved course materials and expert instruction.
Dates/Locations:
No Events
Duration: 2 Days
Course Objectives: At the conclusion of this course, students will be able to:
- Understand the Scrum Flow, the core components of the Scrum framework
- Understand the scope of the Product Owner role in detail
- Understand the scope of the Agile Business Analysis role in coordination with the Product Owner, Scrum Master and Development Team
- Understand the scope of the Scrum Master role at a high level
- Understand the scope of the Scrum Development Team roles
- Document the interactions between the user of a system and the system itself
- Dive into understanding the Agile principles for requirements using user stories in a card, conversation, and confirmation format
Target Student:
- Designed specifically for Agile project team members, product owners, project leaders and business analysts or anyone wanting to understand the Agile Framework.
Comments
Latest comments from students